Systems built on verifiable trust.
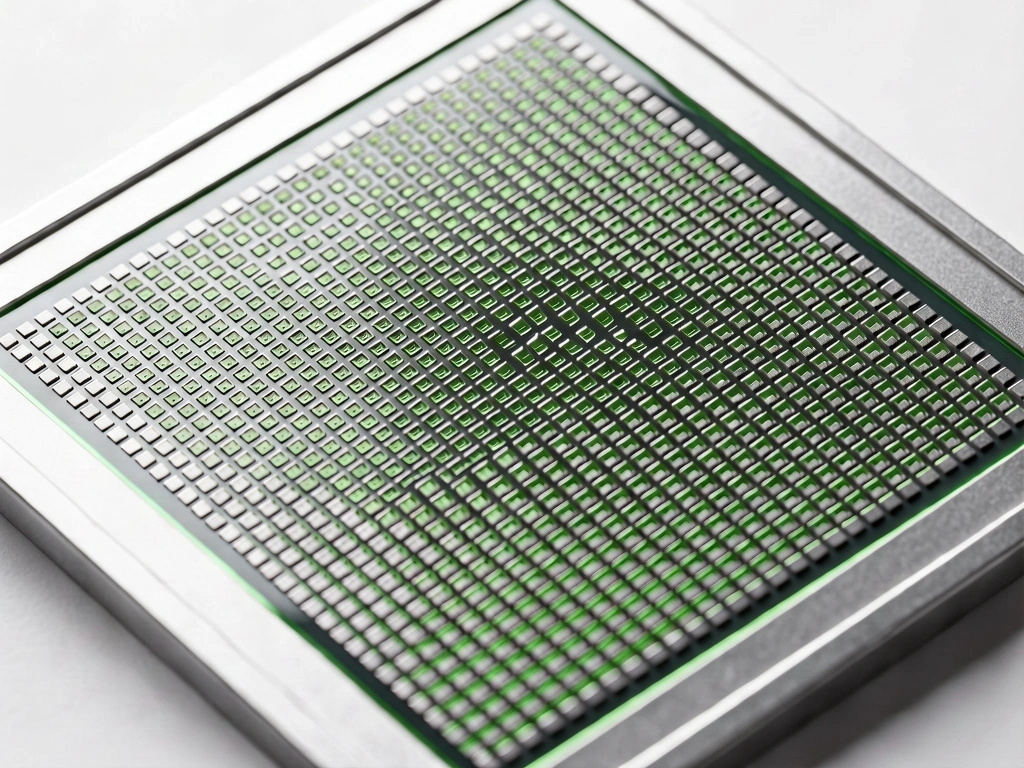
In the landscape of high-velocity logistics and enterprise analytics, data matrix accuracy is not a secondary concern—it is the foundation of operational existence. We maintain rigorous verification protocols to ensure every byte of information serves as a reliable asset.
Verification Protocols
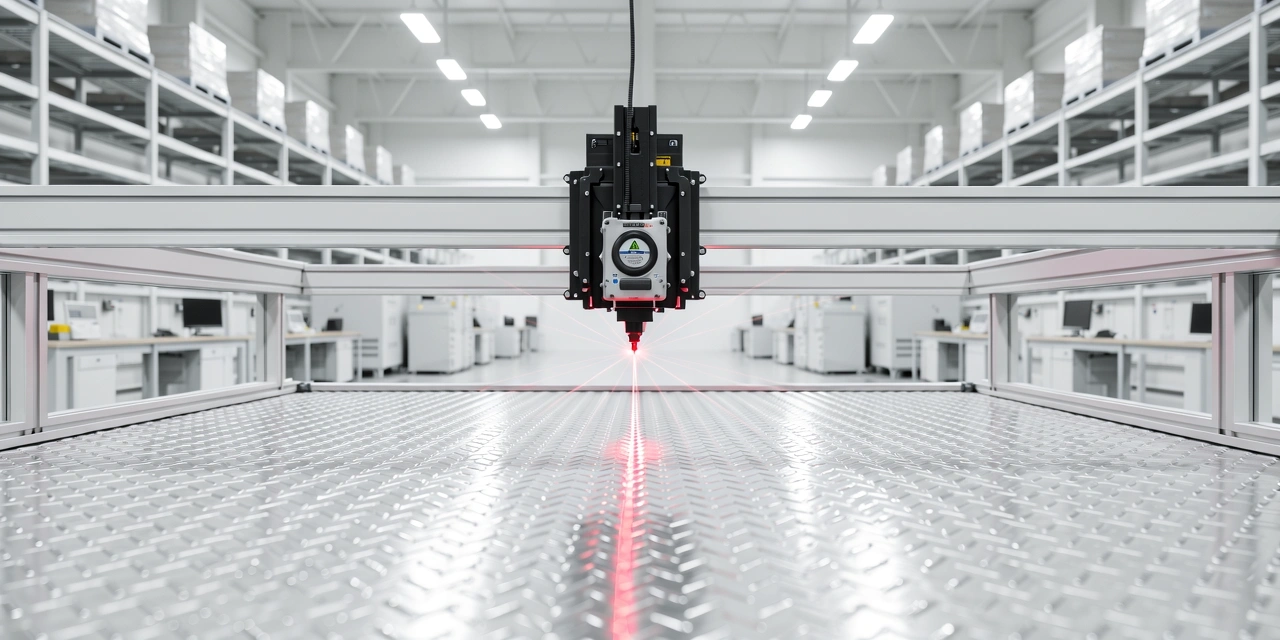
Our multi-layer approach to data matrix systems ensures that physical assets and digital records remain perfectly synchronized. We focus on three core pillars of system integrity.
Technical Standards
Adherence to ISO/IEC 15415 and AIM DPM-1-2006 for barcode quality and data consistency across China-based distribution hubs.
Input Validation & Cleansing
Before any label is printed or any record is committed to the matrix, our systems perform real-time verification. This prevents "data rot" by detecting syntax errors, duplicate identifiers, and incomplete metadata at the source. In a high-volume data matrix environment, early detection saves thousands of hours in potential downstream reconciliation.
- Automated checksum validation
- Cross-reference against legacy GID series
- Real-time anomaly rejection
Hardware-Agnostic Integrity
Trust is built on accessibility. Our systems are engineered to maintain reading integrity across varied hardware—from industrial high-speed scanners to entry-level mobile devices. By normalizing data capture regardless of the scanning environment, we ensure that compliance remains high even in rugged field conditions.

Audit Trail & Forensic Tracking
We don't just store data; we map its journey. Every interaction within the data matrix system is logged with immutable timestamps and operator signatures. This level of system integrity enables rapid forensic audits, allowing managers to identify exactly when and where a discrepancy occurred within seconds.
China Compliance & Regional Standards
Navigating the regulatory landscape in China requires localized expertise. Jade Data Matrix ensures that all tracking systems comply with GB/T national standards and regional industrial data security requirements. We bridge the gap between global efficiency and local compliance mandates.
GB/T 19882 Compatibility
Alignment with domestic identification and data exchange standards for automated systems.
Data Sovereignty
In-region server protocols that respect national data security laws and storage requirements.
Integrity: Frequently Addressed
Verify Your System Integrity Today
Speak with our Shanghai 10 team to review your current data matrix protocols and identify potential vulnerabilities in your tracking lifecycle.